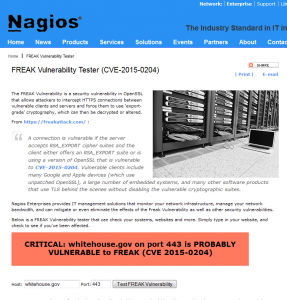
With yesterday’s disclosure of the new SSL/TLS vulnerability dubbed FREAK, we at Nagios decided to take some action to assist the community with a quick and easy tester to help determine if a server is vulnerable to (CVE-2015-0204).
If you are not familiar with the FREAK Vulnerability, here is a brief description from https://freakattack.com/ :
A connection is vulnerable if the server accepts RSA_EXPORT cipher suites and the client either offers an RSA_EXPORT suite or is using a version of OpenSSL that is vulnerable to CVE-2015-0204. Vulnerable clients include many Google and Apple devices (which use unpatched OpenSSL), a large number of embedded systems, and many other software products that use TLS behind the scenes without disabling the vulnerable cryptographic suites.
At Nagios, we take security vulnerabilities very seriously and when possible like to offer the ability to perform a quick check directly from our website.
Enter FREAK Vulnerability Tester (CVE-2015-0204)
Nagios Enterprises provides IT management solutions that monitor your network infrastructure, manage your network bandwidth, and can mitigate or even eliminate the effects of the FREAK Vulnerability as well as other security vulnerabilities.
For most servers that are found to be vulnerable administrators should be able to update the OpenSSL package and then restart the affected services such as httpd.
If your server is running RHEL or CentOS, the following commands will resolve the security vulnerability:
yum update openssl -y
service httpd restart
If you are already using Nagios Core or XI to monitor your infrastructure, this easy-to-use plugin can notify you if your system is susceptible to the FREAK vulnerability.
Download the check_freak Plugin
If you haven’t experienced the benefits of monitoring with Nagios, be sure to check out our products page.